In previous posts I have detailed steps to create Remote Desktop Services application hosting. The flip side of hosting applications using RDS services on Windows Server 2008 R2, is to use RDS services to provide a pool of virtual machines (Windows 7 clients) that users can connect to and use as there own desktops In some of the training schools I attend, this provides a real benefit. Students can connect to a single virtual machine being hosted on Hyper-V. The VM connected to is a member of a pool of VMs. Once the session is over and the student logs off, the VM is returned to a saved Hyper-V snapshot ready to start over again.
This post will detail steps to create a VDI Infrastructure by using different RDS services including Remote
Desktop Virtualization Host Server. At its most basic, Virtual Desktop Infrastructure (VDI) is a deployment design that puts the user desktop on a virtual machine (VM) in the datacenter, rather than on the physical computer at someone’s desk. There are different types of VDI. These include:
- Users can connect to a Virtual Desktop (VD) that has specifically been assigned to that user by using the Remote Desktop Connection Client. The user does not have to know which VM the VD is actually on.
- A pool of desktops available to a set of users on a temporary basis. It is this that we will be trying to create.
Some terms that are often used when discussing VDI include the following:
- The computer that is running the RDC client and that someone sits in front of is called the client.
- The VM that this person is connecting to is the endpoint, or the guest (a guest of the RD Virtualization Host it’s running on).
- Preparing a VM to be used (for example, bringing it out of hibernation) is called orchestration.
- Moving a VM to a new RD Virtualization Host is called placement. Placement is not part of the basic RDS VDI solution but might be supported via a filter plug-in.
The following diagram hopes to expose how a typical VDI 'comes together', and shows you the different RDS services involved. Central to VDI is the role of the
Connection Broker. Clients can make connection requests using a web interface, RDC client etc.

As you can see, clients can connect to the VDI in a number of different ways, some of which have been investigated in earlier posts. My personal favourite is by Remote Desktop Web Access! In all these cases, the request is brokered by the RD Connection Broker. RD Connection Broker works with RDP clients back to RDP 5.2 (which was available for Windows XP SP2 and Windows Server 2003), so the vast majority of Microsoft RDP clients are supported.
To support Microsoft VDI, you’ll need to do the following.
- Install the RD Virtualization Host.
- Install and configure the RD Connection Broker (including the Remote Desktop Session Host in redirector mode on the same computer).
- Install and configure RD Web Access to allow users to discover the VMs.
- Configure the VMs to work with VDI.
- Create pools (and assign personal desktops if required).
We will look at these in turn.
Install the RD Virtualization Host
- Install Hyper-V Server 2008 R2 on a suitable machine ( I am not adding Hyper-V as a role but as an operating system which can be downloaded from Microsoft HERE.
- Once Hyper-V is installed configure it to have suitable NetBIOS name, IP domain membership etc.
- Next enable PowerShell v2 on the system by following an earlier post
- Next you will need to consider management of your Hyper-V server from say a Windows 7 machine. This machine needs to be domain joined and you need to be in as a Domain Administrator. The details can be found by following an earlier post and essentially involves adding the RSAT tools. Don’t forget to also add Server Manager as well because you will need to use this interface in the configuration of the Hyper-V server in addition to Hyper-V management!
- The next big step is to Install Remote Desktop Virtualization Host on your Hyper-V server. An earlier post details how to do this and you will see how you benefit from installing PowerShell which you did in an above step.
Install and Configure the RD Connection Broker and RD Session Host Roles
On a separate server you will need to install the RD Connection Broker role and RD Session Host role. The RDCB is real brains behind the whole thing. The RDSH role is co-resident with RDCB but it doesn’t have to be.
- Log on to the computer as a member of the Domain Administrators group
- Select Start Administrative Tools Server Manager.
- In the Roles Summary section, click Add Roles.
- On the Before You Begin page, click Next.
- Select the Remote Desktop Services check box, and then click Next.
- Select the Remote Desktop Connection Broker and Remote Desktop Session Host role services check box and then click Next
- Click Next on the application compatibility warning
- Select ‘Require Network Level Authentication’ and click Next
- Select ‘Configure Later’ on the Licensing Mode and click Next
- Add Domain Users to allow your users access
- Click next on the Client Experience page.
- Click Install on the confirmation page.
- You will now have to restart the RDCB/RDSH server
Now the two roles have been installed on a server you should continue by configuring the roles.
- On the same server, select Admin Tools
- Select to Remote Desktop Services
- Select Remote Desktop Connection Manager (this is configuring RDCB)
- Select RD Virtualisation Host Servers (shown below) and right click

- Select Add RD Virtualisation Host Server and enter the name of your Hyper-V machine installed earlier
- You should then see the number of virtual machines created on your Hyper-V system. NB. That this works specifically with Hyper-V and no other Hypervisor. The number seen represents all Hyper-V hosted virtual machines be they on or off.
- Select Remote Desktop Connection Manager:ServerName which can be found on the top left part of the window. Their are a number of different configuration settings here (shown below)

- You can change the Display Name. This name will appear in the Web Portal (on RD Web Access). This is shown below:

- On the RD Web Access tab enter the name of the RD Web Access server. If you don’t have one installed I will go though this later, but don’t forget this needs to be added here! The RDWA server account is made a member of the local TS Web Access Computer Group.
- You should see ‘1’ RD Virtualisation Host Server has been added (from step 5 above)
- You can now configure ‘RD Session Host server for redirection’. Select Configure. As this server is also running as a RDSH machine, the same server name should be present. See the diagram below:

- You can also enable redirection for earlier clients as shown above.
- Select Admin Tools
- Select Remote Desktop Services
- Select Remote Desktop Session Host Configuration (this is configuring the RDSH). Remember that both RDSH and RDCB are on the same machine but you could have them running on separate machines.
- Under Remote Desktop Connection Broker on the main page, select ‘Member of Farm in RD Connection Broker’.
- On the RD Connection Broker Tab, select Change Settings
- Ensure that the Virtual Machine Redirection button is selected
- Add the RDCB server name to the RD Connection Broker Server Name field:

- You may receive an error. Ensure that the RDSH computer account has been added to the local computer group ‘Session Broker Computers’ on the RDCB.
- On the Digital Signature tab, you are required to define a suitable certificate. The following post will describe how to create the certificate using Active Directory Certificate Services. The certificate can be shared (I mean it can be the same certificate) amongst all the RD servers. You do this by exporting the certificate. I have gone to some length to explain this in the referred post.
Install and configure RD Web Access
- On a separate server add the RD Web Access Server Role: Log on to the computer as a member of the Domain Administrators group
- Select Start Administrative Tools Server Manager
- In the Roles Summary section, click Add Roles
- On the Before You Begin page, click Next
- Select the Remote Desktop Services check box, and then click Next.
- Select the Remote Desktop Web Access role service check box and then click Next.
- Continue on through the wizard and do not change any of the required components.
- Once the role has been installed, you should import the server certificate that you have used on the RDCB/RDSH server. If you have created this certificate correctly, you should have defined the right Subject Alternative names which will mean that when a user connects to the RDWA server using the web portal, no errors should occur.
- Once the certificate is in place reboot the server.
- Once restarted, select Admin Tools
- Select Remote Desktop Services
- Select Remote Desktop Web Access Configuration
- Sign in as Administrator and select configure. The interface is shown below:

- Select the RD Connection Broker and add the RDCB name as the Source Name.
- You should not receive any errors if you have added the RDWA computer account to the local TS Web Access Computer Group on the RDCB server (see step 9 of Install RDCB and RDSH above)
Configure the VMs to work with VDI
In my test infrastructure I have installed two Windows 7 virtual machines on Hyper-V. The following configuration is made on both of course.
- Each machine needs to be joined to the domain
- Click Start, Control Panel, System and Security, click on System, Advanced System Settings and select the Remote tab. Select the radio button that allows connections using Network Level Authentication. Also select the Select Users button. Define which users should have remote access. You will most likely add Domain Users.

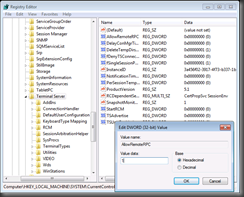
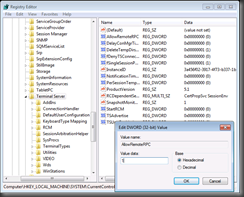
- You will then need to enable RemoteRPC. Remote Procedure calls (RPCs) allow other processes to connect with the operating system. They’re required to allow the VM Host Agent to wake up the VM. To allow RPC connectivity,
set the value of AllowRemoteRPC to 1 in the location HKLM/System/CurrentControlSet/Control/Terminal Server.
- We next should configure each Windows 7 machines firewall to allow for Remote Desktop. Select Start, type ‘Fire’ and from the list given select ‘Allow Program Through the Windows Firewall’. Select Change Settings and select ‘Remote Desktop’ on the Domain Profile

- You will next need to configure RD virtualization host RDP permissions. This is a little tricky. I have found that running a PowerShell script to be the easiest solution. The script can be found here. A copy can be found at the bottom of this post. Just copy the script to a text document and save as a file with a PS1 extension.
- Select Start and simply type ‘Power’ in the search field. Select the PowerShell icon that appears (you should run this as an Administrator).
- Type the cmdlet set-executionpolicy unrestricted
- Locate the directory that your script is in (created in step 5) and type the following cmdlet: .\yourscript.ps1 –RDVHost yourdomain\RD Virtualisation Server replacing the script, domain and RD virtualisation server with your own

- Remember to do this on each Windows 7 machine!
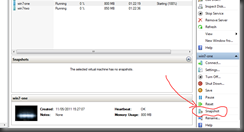
- Your next move is to take snapshots of the virtual machines running on your Hyper-V system. Make sure you log off each Windows 7 system. Select each Windows 7 virtual machine and select snapshot as indicated below:
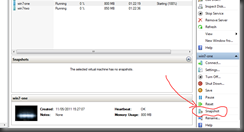
- Once each snapshot has been taken, ensure that each one is renamed with RDV_Rollback in the snapshot name:

- The above procedure will automatically roll the VM back to this snapshot after the user logs off.
Create VM Pools
Our next task is to create a VM Pool on the RD Connection Broker.
- Log on as Domain Admin on the RD Connection Broker.
- Open the RD Connection Manager from the RD Services in Admin Tools.
- Select RD Virtualisation Host Servers
- Under Actions on the right hand side, select ‘Create Virtual Desktop Pool’
- Click Next on the Welcome screen
- You should now see all of your virtual machines created on your Hyper-V system.
- Using CTRL key select each Windows 7 machine. Click Next
- Enter a name for the pool. Something like ‘Windows 7 Pool’.
- Enter the name for the Pool ID. Something like ‘Pool1’
How Does the User Connect?
A user can connect to the pool using the web portal hosted on the RD Web Access Server.
- Opens a browser and types the URL of the RDWA server followed by /owa (E.g. https://RDWAserver/rdweb)
- Sign in as an ordinary user
- You should now see the Windows 7 pool created above:

- Select the pool and provide the password